1. Namespace 생성
kevin@k8s-master:~$ kubectl create ns testing
namespace/testing created
kevin@k8s-master:~$ kubectl get ns testing
NAME STATUS AGE
testing Active 9s
kevin@k8s-master:~$ kubectl create deployment nginx-pod --namespace testing --image=nginx:latest --replicas=1
deployment.apps/nginx-pod created
kevin@k8s-master:~$ kubectl expose deployment nginx-pod --namespace testing --name=nginx-svc --port=80 --target-port=80 --type=ClusterIP
service/nginx-svc exposed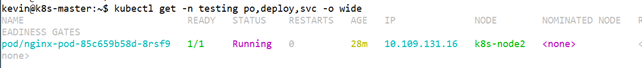
2. pod 및 service 생성
kevin@k8s-master:~$ kubectl create ns testing
namespace/testing created
kevin@k8s-master:~$ kubectl get ns testing
NAME STATUS AGE
testing Active 9s
kevin@k8s-master:~$ kubectl create deployment nginx-pod --namespace testing --image=nginx:latest --replicas=1
deployment.apps/nginx-pod created
kevin@k8s-master:~$ kubectl expose deployment nginx-pod --namespace testing --name=nginx-svc --port=80 --target-port=80 --type=NodePort
service/nginx-svc exposed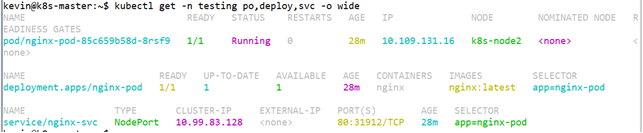
3. Ingress 생성
kevin@k8s-master:~$ vi test-ingress.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: nginx-ingress
namespace: testing
annotations:
nginx.ingress.kubernetes.io/ssl-redirect: "true"
nginx.ingress.kubernetes.io/force-ssl-redirect: "true"
spec:
tls:
- hosts:
- cks.test.com
secretName: tls-secret
rules:
- host: cks.test.com
http:
paths:
- path: /
pathType: Prefix
backend:
service:
name: nginx-svc
port:
name: http
kevin@k8s-master:~$ kubectl apply -f test-ingress.yaml
ingress.networking.k8s.io/nginx-ingress create4. TLS 생성 및 TL-Ssecret 생성
kevin@k8s-master:~/tlstest$ openssl genrsa -out cks.test.com.key 2048
Generating RSA private key, 2048 bit long modulus (2 primes)
.............................................................................................................................+++++
...............................................................................+++++
e is 65537 (0x010001)
kevin@k8s-master:~/tlstest$ openssl req -new -key cks.test.com.key -out cks.test.com.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:
State or Province Name (full name) [Some-State]:
Locality Name (eg, city) []:
Organization Name (eg, company) [Internet Widgits Pty Ltd]:
Organizational Unit Name (eg, section) []:
Common Name (e.g. server FQDN or YOUR name) []:cks.test.com
Email Address []:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
kevin@k8s-master:~/tlstest$
kevin@k8s-master:~/tlstest$ openssl req -in cks.test.com.csr -noout -text
Certificate Request:
Data:
Version: 1 (0x0)
Subject: C = AU, ST = Some-State, O = Internet Widgits Pty Ltd, CN = cks.test.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
RSA Public-Key: (2048 bit)
Modulus:
Exponent: 65537 (0x10001)
Attributes:
a0:00
Signature Algorithm: sha256WithRSAEncryption
kevin@k8s-master:~/tlstest$ openssl x509 -req -days 365 -in cks.test.com.csr -signkey cks.test.com.key -out cks.test.com.crt
Signature ok
subject=C = AU, ST = Some-State, O = Internet Widgits Pty Ltd, CN = cks.test.com
Getting Private key
kevin@k8s-master:~/tlstest$ openssl x509 -in cks.test.com.crt -text -noout
Certificate:
Data:
Version: 1 (0x0)
Serial Number:
1a:dd:55:b6
Signature Algorithm: sha256WithRSAEncryption
Issuer: C = AU, ST = Some-State, O = Internet Widgits Pty Ltd, CN = cks.test.com
Validity
Not Before: May 3 01:55:58 2023 GMT
Not After : May 2 01:55:58 2024 GMT
Subject: C = AU, ST = Some-State, O = Internet Widgits Pty Ltd, CN = cks.test.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
RSA Public-Key: (2048 bit)
Modulus:
00:e7:0f:07:d2:0a:aa:e6:4b:19:fe:e4:0a:e4:e0:
생략
9d:85
Exponent: 65537 (0x10001)
Signature Algorithm: sha256WithRSAEncryption
14:55:36:50:e5:ed:f8:50:00:f5:8a:d6:f4:f5:f1:97:e2:4e:
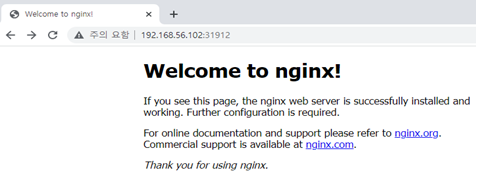
생략5. secret 생성
kevin@k8s-master:~/tlstest$ kubectl create secret tls tls-secret --key=cks.test.com.key --cert=cks.test.com.crt
service는 NodePort로 변경해주었습니다 "kubectl edit 명령어 사용"
6. 확인
kevin@k8s-master:~/tlstest$ curl 192.168.56.102:31072
<!DOCTYPE html>
<html>
<head>
<title>Welcome to nginx!</title>
<style>
html { color-scheme: light dark; }
body { width: 35em; margin: 0 auto;
font-family: Tahoma, Verdana, Arial, sans-serif; }
</style>
</head>
<body>
<h1>Welcome to nginx!</h1>
<p>If you see this page, the nginx web server is successfully installed and
working. Further configuration is required.</p>
<p>For online documentation and support please refer to
<a href="http://nginx.org/">nginx.org</a>.<br/>
Commercial support is available at
<a href="http://nginx.com/">nginx.com</a>.</p>
<p><em>Thank you for using nginx.</em></p>
</body>
</html>
'Kubernetes (k8s)' 카테고리의 다른 글
| [k8s] Rollout Canary -- workbook (1) | 2023.05.21 |
|---|---|
| [k8s] VPA (Vertical Pod Autoscaler) 설치 및 실습 (1) | 2023.05.16 |
| [k8s] Deploy & Pod Scale (1) | 2023.04.24 |
| [k8s] Persistent Volume (1) | 2023.04.20 |
| [k8s] Resource 사용량 확인을 위한 Metric Server 설치 (1) | 2023.04.18 |




댓글